In a world increasingly dominated by the digital realm, the invisible armor of cyber security is what stands between us and a host of cyber threats poised to exploit our every move. This article is your gateway to understanding the multifaceted world of cyber security, dissecting the 7 pivotal layers that form the bulwark against the ever-evolving landscape of cyber threats. Each layer is a beacon in the storm of digital vulnerability, offering unique protection mechanisms to shield your precious digital territories.
7 Layers of Cybersecurity
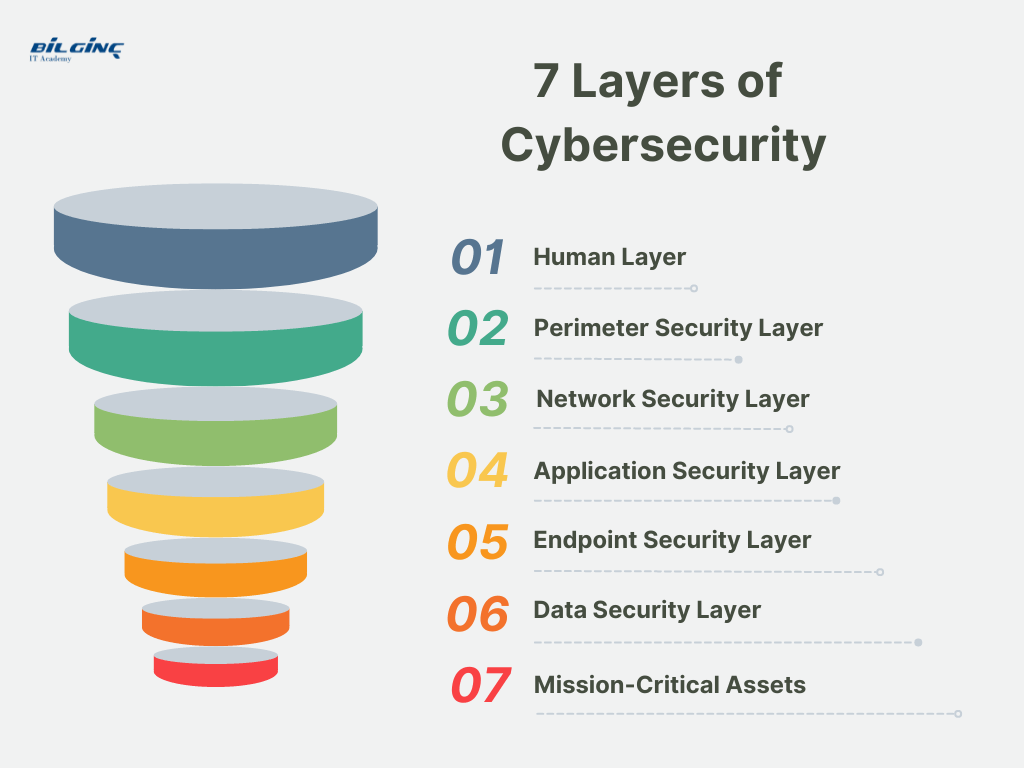
1. Human Layer:
The human layer, often regarded as the most vulnerable layer, focuses on the human element within an organization. It involves implementing practices and policies that ensure that employees, contractors, and other users do not fall victim to phishing attacks and other security threats due to human error or lack of knowledge.
Examples of human layer security measures include security awareness training, strong password policies, and multi-factor authentication, ensuring that users can identify and respond appropriately to security threats.
2. Perimeter Security Layer:
Perimeter security layer is akin to the walls of a fortress. It serves to protect the network by controlling incoming and outgoing network traffic based on an organization's previously established security policies. At its core, it involves implementing firewalls, intrusion detection systems (IDS), intrusion prevention systems (IPS), and VPNs to create a barrier between your secure internal network and untrusted external networks such as the internet.
An example of how this works is a firewall that filters incoming traffic to allow or block packets based on the organization’s security policies, thus preventing unauthorized access to networked resources.
3. Network Layer:
The network layer is crucial in managing and protecting the communication between applications and devices on your network. This layer employs various security measures and controls to prevent attackers from intercepting and tampering with information as it travels over the network. Examples of network layer security include the use of secure protocols like HTTPS, employing network segmentation to separate sensitive parts of the network from less sensitive ones, and implementing security solutions like anti-malware and antivirus software to monitor and analyze network traffic for malicious activity and unauthorized access.
The network layer is pivotal in the cyber security landscape as it serves as the communication bridge connecting various components within a network, facilitating data transfer between them. It holds immense importance because it is inundated with a multitude of information exchanges, making it a lucrative target for cyber adversaries aiming to intercept, modify, or disrupt the data flow. By securing the network layer through strategies like encryption, secure protocols, and robust network architectures, organizations can ensure the integrity, availability, and confidentiality of the transmitted information, thereby protecting against unauthorized access and potential cyberattacks, and maintaining seamless and secure organizational operations.
4. Application Security Layer:
This layer focuses on keeping software and devices free of threats. Secure coding practices are vital here, as vulnerabilities in the application can serve as entry points for cyber threats. Examples of application security measures include regular security scanning and testing to identify and remedy vulnerabilities and employing application security solutions like Web Application Firewalls (WAFs) to protect against threats such as SQL injection and Cross-Site Scripting (XSS).
Cyber Security Training Catalogue
5. Endpoint Security Layer:
The endpoint security layer concentrates on safeguarding the individual devices that connect to the network, like computers, smartphones, and tablets. Since these endpoints serve as access points to the network, securing them is crucial. An example of endpoint security is employing antivirus programs and endpoint detection and response (EDR) solutions to monitor, detect, and block malicious activities and threats on endpoints, ensuring that even if a device is compromised, the threat does not propagate through the network.
6. Data Security Layer:
This layer is dedicated to protecting the data residing in the network, focusing on maintaining its confidentiality, integrity, and availability. Encryption is a prime example of a data security measure, where sensitive data is converted into a coded format to prevent unauthorized access. Another example is employing backup solutions and establishing robust access controls to safeguard data from loss, exposure, and unauthorized access, ensuring only authorized personnel can access sensitive information.
A Comprehensive Guide to Cloud Data Security
7. Mission-Critical Assets:
This layer focuses on safeguarding assets that are crucial to an organization's operations and business continuity. These could include proprietary software, sensitive customer data, or essential hardware. Protection strategies here involve implementing layered defenses like firewalls, intrusion detection and prevention systems, and robust access controls. For instance, regularly updating and patching mission-critical applications ensures that vulnerabilities are addressed, minimizing the risk of exploitation and ensuring the uninterrupted functionality of essential assets.

In the rapidly evolving domain of cyber security, possessing a nuanced understanding of the multi-layered defense mechanisms is indispensable. The proficiency in securing each layer not only opens up a plethora of cybersecurity jobs but also promises a lucrative salary. Attaining a cybersecurity certification is a significant step towards becoming a formidable cybersecurity engineer or a meticulous cybersecurity analyst. By enrolling in a cyber security course or a comprehensive cyber security bootcamp, individuals and corporates can acquire hands-on training, essential in navigating the multifaceted landscape of cyber threats effectively.
At Bilginç IT Academy, we are proud to offer a plethora of cyber security courses tailored for both individuals and corporates, aiming to bridge the knowledge gap in this critical field. With nearly 30 years of seasoned experience in IT training, we are committed to delivering excellence and enhancing your professional journey in cybersecurity. Whether you are an individual aiming to delve deeper into the realms of cyber security or a corporate entity seeking to fortify its defenses, our customizable training sessions can be organized at any preferred location, ensuring an enriched learning experience that aligns with your unique needs and aspirations. Embrace the journey towards becoming a cyber-savvy professional and fortify your skills to navigate the digital world securely and proficiently.